Analyze a docker image
We support scanning a docker image to analyze the compositions of this image and vulnerability license malware information about this image.
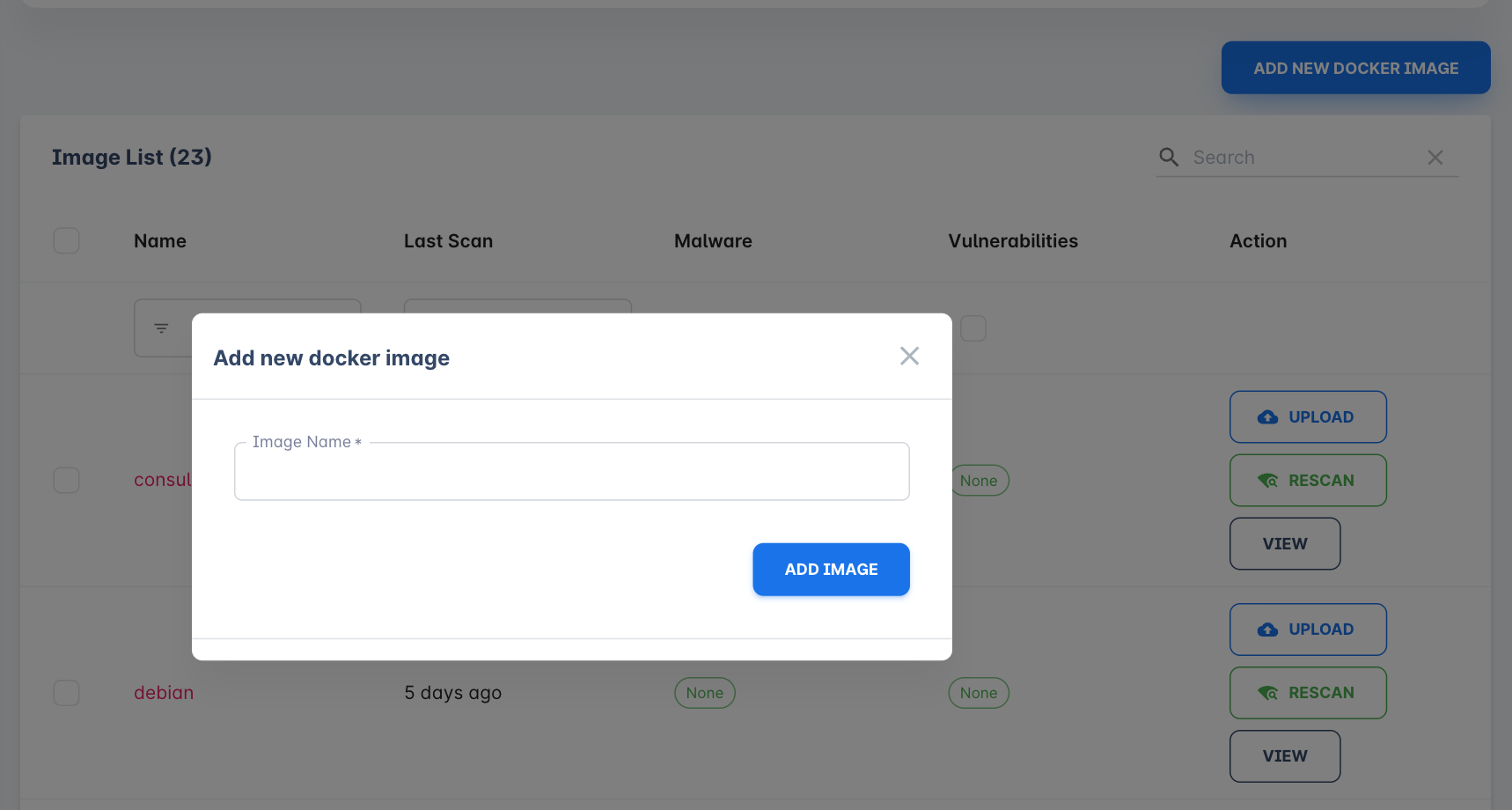
Create image
Click the "Add new docker image" button on the On-premises - Images page. Input a meaningful name then the image is created.
Upload image
After the image is created, you have to upload the image file then we can start to scan this image. You'll see instructions for exporting the docker image file when you click the upload button.
After the image is uploaded we'll start to scan it.
Scan result
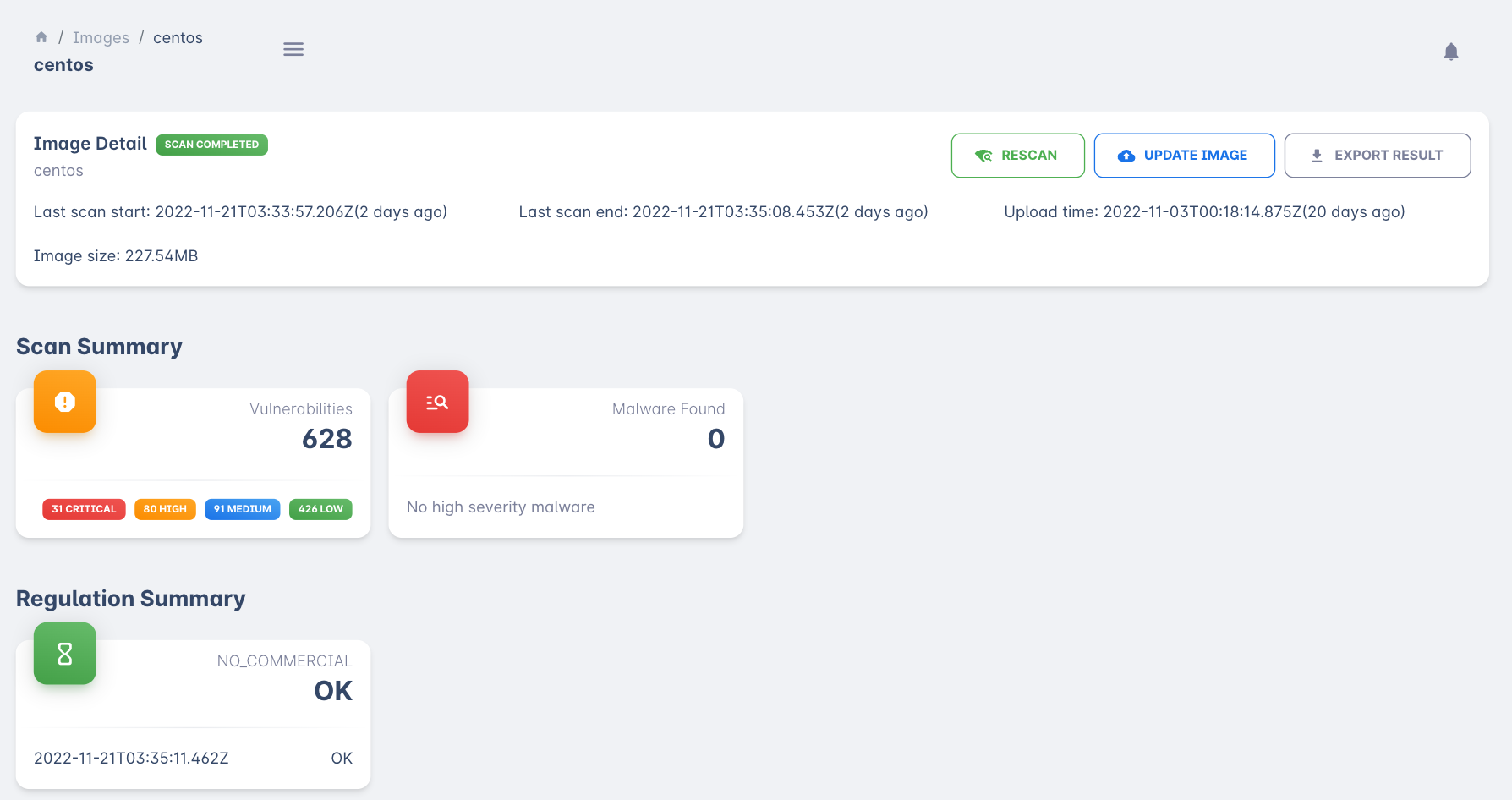
You'll see a few sections for an image.
Basic information
Shows the basic image information like scan time, upload time, image size, scan status, etc. There are a few actions you can do in this section.
Rescan
Trigger a rescan on this image to reflect the latest result. usually, you don't need to do this since when you update the image file or we updated our knowledge base system the image will rescan automatically.
Update Image
Click this button when you have an updated version of your docker image.
Export result
You can export the report to a PDF file for print or email.
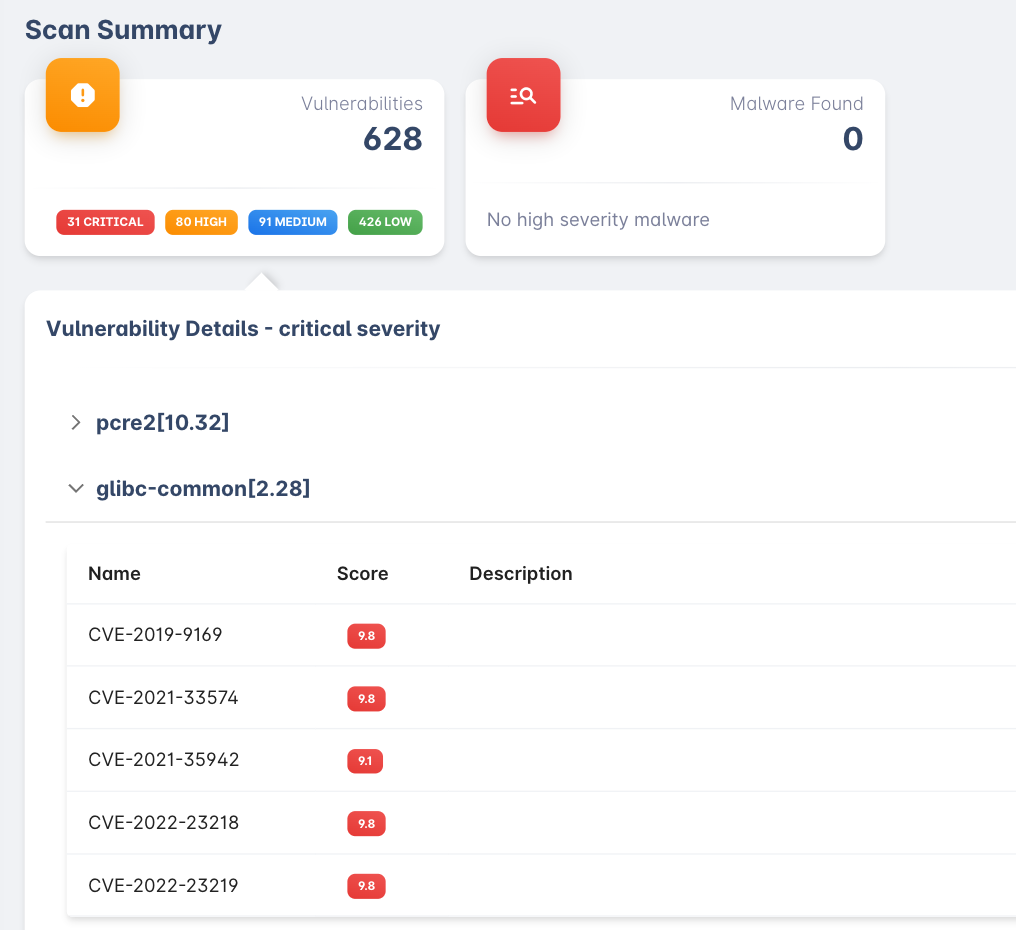
Scan Summary
This section shows vulnerability and malware we found in the image. You can click on the panel to see the details of it.
Regulation summary
The regulation policy executes results for this image. See more about regulation on the docs.
Static Analysis Result
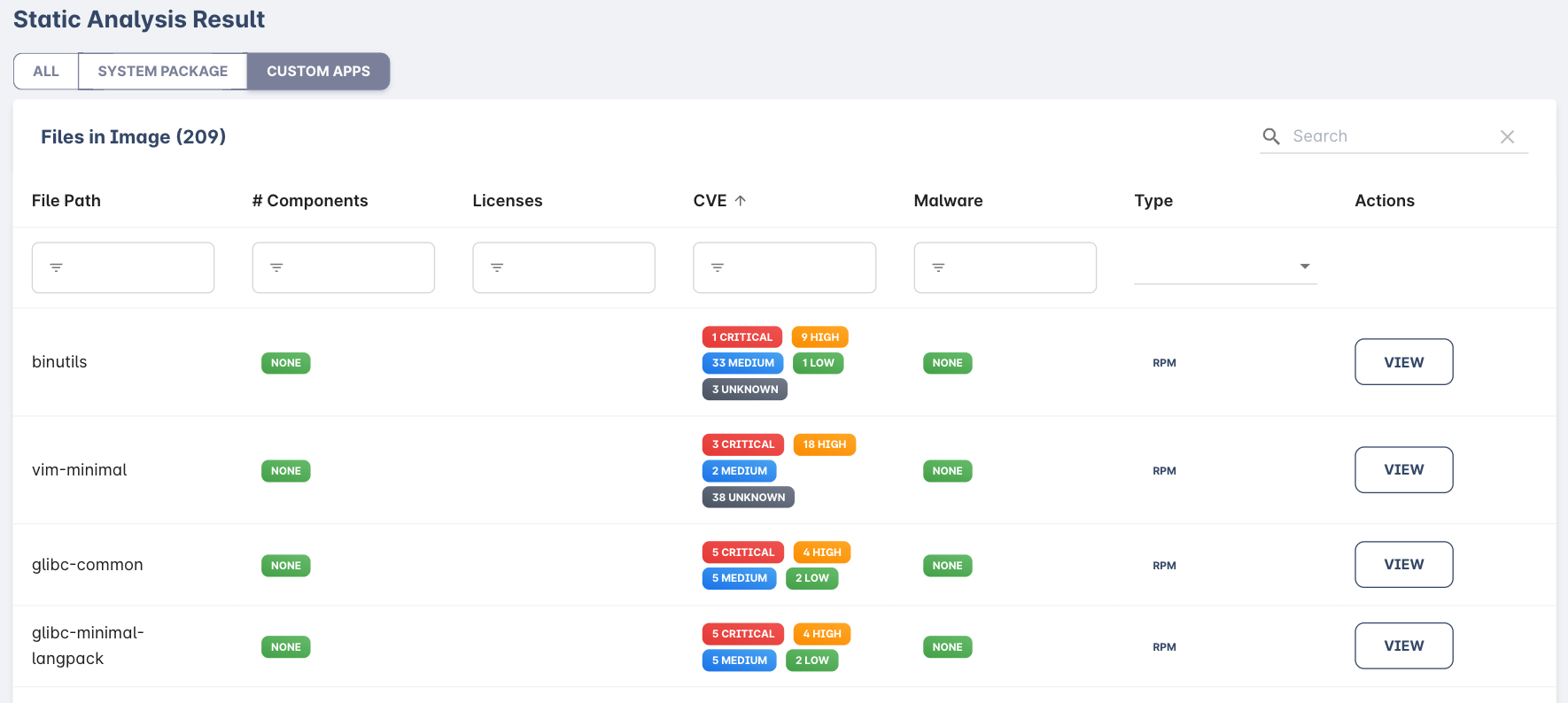
This section shows the file and components analysis result. you can see which file is included in your docker image and the components license or issues inside this file. You can also filter files by system package or custom apps filter.
File SBOM info
Each file inside the static analysis result table is clickable. You can click to check the file details.
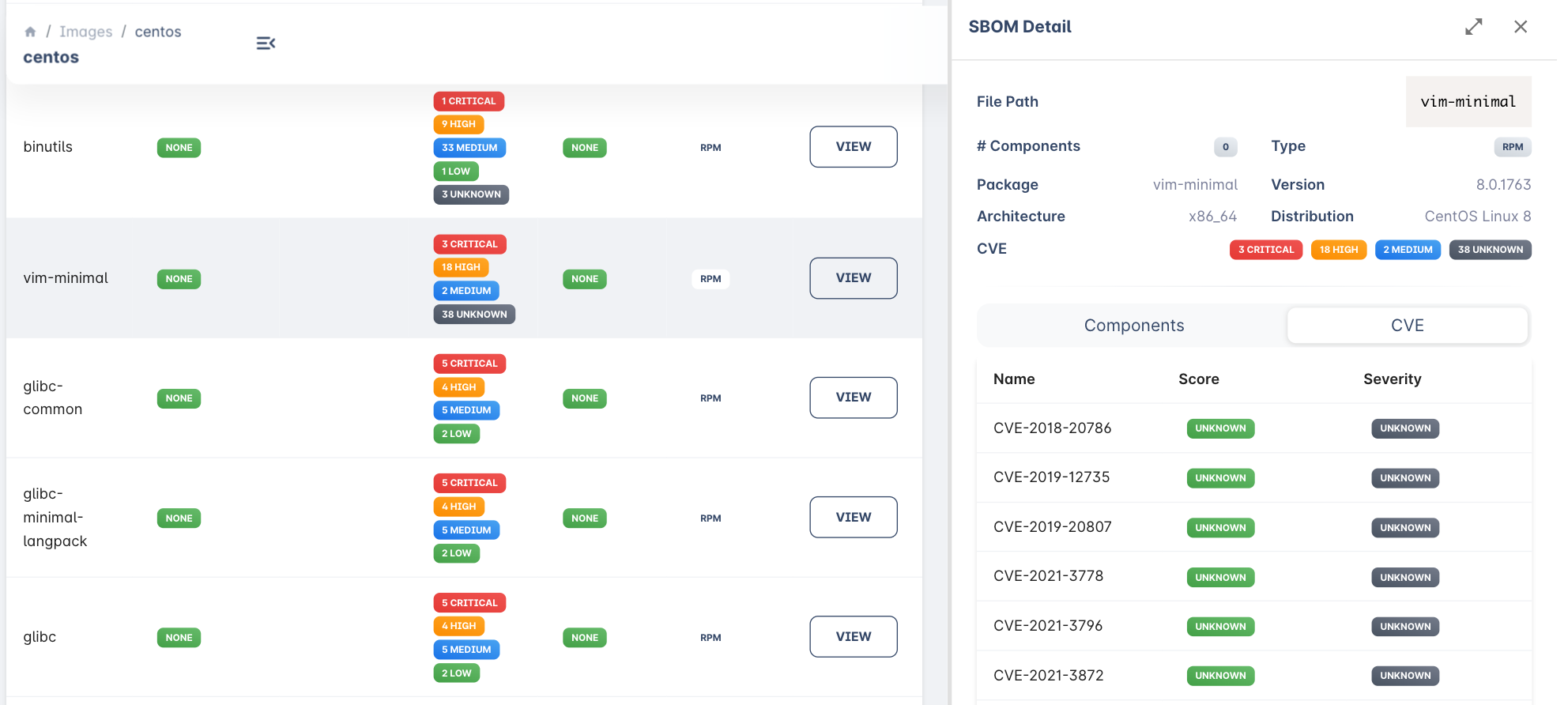
Inside the right side SBOM detail panel, you can see the basic information about the file and components inside this file. Also a CVE list we found in this file.
Export file SBOM
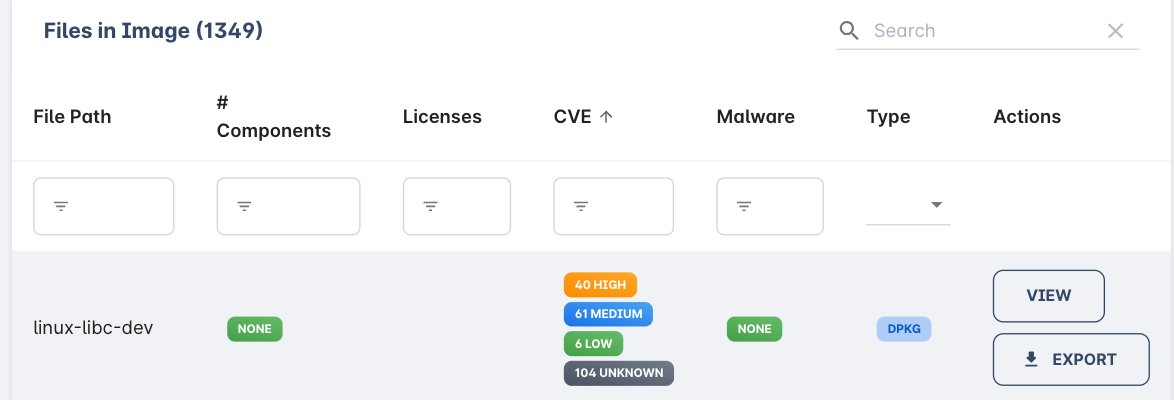
We support exporting SBOM info in CycloneDX format. After export, you can import it into another platform like Dependency Track. If you see an export button in the actions row that means the file SBOM is generated and ready to export.
Updated 16 days ago
