Introduction
Simplify Your Software Asset Security Management with SBOM insights
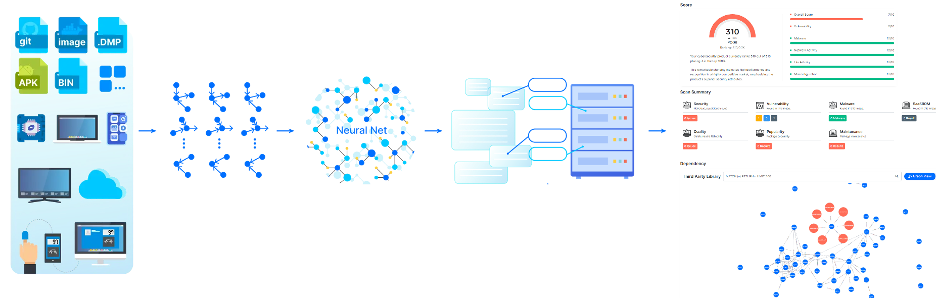
Figure 1: Overview of DeepAsset
Software asset security management is challenging due to the sheer volume and diversity of assets across multiple platforms, environments, and versions, making comprehensive tracking difficult. Vulnerability management adds complexity, as assets accumulate risks over time, and prioritizing remediation without clear risk context can be resource-intensive. The widespread use of open-source components further increases risk, as vulnerabilities in third-party libraries may go undetected or unpatched. Lastly, collaboration across security, IT, and development teams is often hindered by differing priorities and a lack of standardized tools, delaying responses and weakening overall security. Robust monitoring, automation, and cross-department alignment are essential to secure assets effectively.
DeepAsset utilizes AI technologies to simplify software asset security management with SBOM insights. It generates a Software Bill of Materials (SBOM) directly from executables and performs comprehensive asset management to reveal what your software depends on and contains, regardless of whether the source code is available or not.
DeepAsset (Figure 1) provides the following core features.
- End-to-end SBOM Management. It covers the complete lifecycle of SBOMs, including generation, distribution, and monitoring. It enables users to import software assets and automatically generates SBOMs without the need for source code. Efficiently sharing the SBOM with relevant stakeholders such as customers, partners, and regulatory bodies is facilitated. Additionally, continuous monitoring of the software supply chain allows for tracking changes, vulnerabilities, and updates related to the listed components. This ensures staying informed about security advisories, patches, and vulnerabilities to proactively address risks and maintain the integrity of the supply chain.
- License Analysis. Effortlessly manage open-source licenses with DeepAsset. Our platform covers 550+ licenses, simplifying compliance and decision-making. Stay informed, stay compliant.
- Real-Time Vulnerability Assessment. Discover known vulnerabilities embedded within your software, while also enjoying the peace of mind that comes from our continuous real-time monitoring of emerging threats. keeping you informed, protected, and always a step ahead.
- In-Depth Reporting. Stay on top of your software landscape. Generate precise executive summaries, daily/monthly overviews, and attestation reports, all tailored for your software assets. Get insights on threats, the status of your assets, and more, ensuring comprehensive visibility and informed decision-making.
Red Team
Besides our software solutions, we also provide red team services. Our red team comprehensively evaluates your software assets to uncover hidden vulnerabilities, malware, license violations, and more. We also perform routine evaluations to keep your software ‘healthy’.
Pricing Plan
| Plan | Free | Basic (Monthly) | Pro (Monthly) | Premium |
|---|---|---|---|---|
| Price | $0 | $200 | $1,000 | Contact Us |
| # of Assets | 10 | 100 | 1000 | TBD |
| SBOM Registry | 10 | 50 | 500 | TBD |
| # SBOM Subscribers | Unlimited | Unlimited | Unlimited | Unlimited |
| Continuous Monitor | Y | Y | Y | Y |
| Smart Query | Y | Y | Y | Y |
| Integrations (webhook, Jira, GitHub, etc.) | Y | Y | Y | Y |
| Vulnerability Assessment | Y | Y | Y | Y |
| Malware Detection | Y | Y | Y | Y |
| License Check | Y | Y | Y | Y |
| On-Premise Deployment | N | N | N | N |
| Tech Support (Business Days) | N | 5 | 3 | 1 |
Add-on Service
Red Team: Software Supply Chain Security Assessment
| Assessment Type | Price |
|---|---|
| Initial Assessment | $20K |
| Routine Assessment | $5K |
Demo Account
Log into the demo account below to explore the platform's features.
URL: DeepAsset
Username: [email protected]
Password: 5aU2umLSDmDvfue*
Updated about 1 month ago
